A Story of Crypto Wars, the Growth on the Internet, and possible future Regulations
 The discussion about how to tackle end-to-end encryption (E2EE) and how to reconcile it with surveillance is almost 30 years old. The very first Crypto War was sparked by the Comprehensive Counter-Terrorism Act of 1991 (no, there is no mention of cryptography in it, because it was the first draft of a series of legislative texts dealing with a reform of the US justice system; have a look at the author of the act). In the following years things like strong cryptography, export bans on mathematics, or the creation of Phil Zimmerman’s Pretty Good Privacy (PGP) were a follow-up. Even the proposal of having the Clipper chip present in telecommunication devices and the concept of key escrow was discussed in the wake of the reform. Sometimes laws have to grow with the technology. All discussion since the 1990s have evolved around the same principles. Only the wordings were – and are – different. Euphemisms don’t hurt, right?
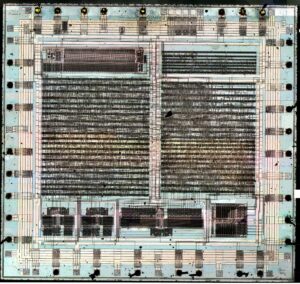
The discussion about how to tackle end-to-end encryption (E2EE) and how to reconcile it with surveillance is almost 30 years old. The very first Crypto War was sparked by the Comprehensive Counter-Terrorism Act of 1991 (no, there is no mention of cryptography in it, because it was the first draft of a series of legislative texts dealing with a reform of the US justice system; have a look at the author of the act). In the following years things like strong cryptography, export bans on mathematics, or the creation of Phil Zimmerman’s Pretty Good Privacy (PGP) were a follow-up. Even the proposal of having the Clipper chip present in telecommunication devices and the concept of key escrow was discussed in the wake of the reform. Sometimes laws have to grow with the technology. All discussion since the 1990s have evolved around the same principles. Only the wordings were – and are – different. Euphemisms don’t hurt, right?
The current state of affairs has not changed. E2EE is a desirable property of secure communication. This is true for voice calls, and it is true for any data transmission. This is why TLS v1.3 took a while, because eliminating meet-in-the-middle attacks and algorithms using forward secrecy were highly contested. There was even a proposal of „trusted“ proxies by AT&T that sit in between the secure communication channel having access to the content by decrypting and re-encrypting. Trust is not something you can create out of thin air. The update of the TLS protocol suite was long overdue. This was clear to anyone responsible for deploying or researching cryptography. Furthermore E2EE leaves no room for ambiguity. Either only the endpoints have the keys, or they don’t. If unknown or untrusted third parties have access to the key material, then you have something other than E2EE. It’s as simple as that. Bear in mind that bugs in the implementation do not count. Bugs are (yet) no mandatory part of standards or regulations.
The current article that sparked the tweet storm has its roots in the EU bodies that address technologies for secure communication. Messenger apps on smartphones are the main argument for third parties requesting means to get access to the content. The problem with messengers is the different architecture. Signal, WhatsApp, Telegram, Threema, Wickr, and all other have a different approach and a widely different view of how secure communication should be. Some messengers leave the control of the E2EE features to the messenger infrastructure. Others are part of a social media platform and allow to mine metadata for identifying clusters of „friends“ or communication profiles. Clearly this is not secure communication.
The bigger picture are the visions of the digital world. The Internet has created a lot of technologies and convenient tools. Below the surface the Crypto Wars never left. You have to be very vigilant not to be lured by soft language into the dead ends of surveillance. The EU has a vision for the future, too. To quote from a study called New Developments in Digital Services:
A European firewall/cloud/internet would foster a digital ecosystem in Europe based on data and innovation. … Technologically, it would require a top-level infrastructure, high-speed 5G or a 6G data network and a firewall. … Like the Chinese firewall, this European internet would block off services that condone or support unlawful conduct from third party countries.
Basically this vision can turn into a walled garden where the concept of universal computing might be missing. In this case we will have a lot more to worry about than the lack of E2EE.
