Translated Article: EU Prosecutors call for Security Holes in 5G Standards
EU-Strafverfolger fordern Sicherheitslücken in 5G-Standards for fm4 by Erich Moechel
 The telecoms are to be forced to align the technical design of their 5G networks with the monitoring needs of the police authorities. In addition, security holes in the 5G protocols are required to enable monitoring by IMSI catchers.
The telecoms are to be forced to align the technical design of their 5G networks with the monitoring needs of the police authorities. In addition, security holes in the 5G protocols are required to enable monitoring by IMSI catchers.
Gilles de Kerchove, EU counter-terrorism coordinator, warns against the planned security standards for the new 5G mobile networks. The reason for this are neither network components of the Chinese manufacturer Huawei, nor technical defects. De Kerchove’s warnings are directed against the planned high degree of network security, according to an internal document of the EU Council of Ministers, available to ORF.at.
These measures to protect against criminals as well as the planned 5G network architecture stand in the way of the installation of backdoors for police and secret services. The telecoms should therefore build their networks in a way that meets the requirements of the prosecutors, demanded de Kerchove. Similarly, the 5G security protocols should also provide vulnerabilities for so-called IMSI catchers.
„Surveillance as a Service“
These demands can be found in a document from the Council of Ministers on the 6th of May, addressed to the usual addressees, namely to working groups of police and security authorities and to the delegations of the Member States. The telecoms could be forced by national legislation “to meet other requirements than those prescribed in the standards,” it says. However, it would be preferable “to implement these requirements already in the standards.”
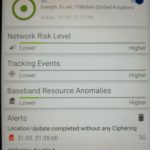
In fact this means that the required security gaps – including access mechanisms for the prosecutors – should be anchored so deeply in the 5G security standards themselves that all individual security measures of the telecoms would not affect the network’s ability to be monitored. Thus, they require nothing less than “Surveillance as a Service”, ie a separate cloud service of the 5G operator for the prosecutors, which should have priority over the services of the network operator.
“Fragmented” is the new “decentralized”
On the one hand, the problem with encryption in the 5G networks will worsen in the medium term, de Kerchoves’ text continues. The main problem, however, is “5G’s fragmented and virtual architecture,” but especially the “network slicing” technology. What is called “fragmented” from the perspective of the authorities is an element of the decentrally organized 5G cloud called “multi-access edge computing”. To achieve latencies of less than one millisecond, as formalised in the 5G specification, in 5G networks as many functions as possible are outsourced to the peripherals.
The data gets also already processed in the segment in which a smartphone has logged in, and only a part of it ends up at the headquarters of the telecoms. To date all monitoring interfaces from GSM to LTE are installed there. In addition, instead of dealing with a handful of telecoms per member state, one now has to deal with a large number of virtual providers, and then there is the further possibility that parts of these services can be outsourced to other EU countries. De Kerchove’s assumption is quite realistic, as all three mobile operators in Austria are part of multinational corporations. Where the data is actually processed does not matter in a cloud network.
How the 5G Operators should build their Networks
The somewhat less realistic conclusion of de Kerchove: “A basic requirement for 5G providers (…) should be that they can meet the needs of prosecutors, even if they have to involve their partner companies abroad.” Since it might not be possibly to deliver “the normally available metadata” completely – due to the described security measures and the network architecture – they would have to “structure their network in a way that the geographical data is always available”.
Here, telecoms are required to align the architecture of upcoming 5G clouds with law enforcement needs, while operators’ priorities are low latency, security, and data transmission efficiency. And another security measure of the 5G networks is a thorn in the side of the prosecutors, namely the “strict authentication processes”. This refers to the automatic authentication of 5G base stations to smartphones with each login process.
The bad old IMSI catchers
Since the beginning mobile radio protocols have had a security hole by design, which has existed since the introduction of GSM. The base station does not need to identify itself as a legitimate network component to a logging in cell phone. This gap has since been exploited by so-called IMSI catchers, which are nothing more than false base stations that attract smartphones in the vicinity to, for example, disable their encryption. Police authorities use IMSI catchers for shading suspects in order to locate their smartphones on an ongoing basis.
However, IMSI catchers are also the most popular espionage devices, part of the standard inventory of every secret service. During the last ten years, the problem had become endemic, especially around international conferences, so all major manufacturers of mobile equipment released devices for identifying and neutralizing “false base stations”. Against these “IMSI catcher-catchers” this longstanding monitoring method is without chance.

 The telecoms are to be forced to align the technical design of their 5G networks with the monitoring needs of the police authorities. In addition, security holes in the 5G protocols are required to enable monitoring by IMSI catchers.
The telecoms are to be forced to align the technical design of their 5G networks with the monitoring needs of the police authorities. In addition, security holes in the 5G protocols are required to enable monitoring by IMSI catchers.