Translated Article: Germany becomes the Federal Trojan Republic
Deutschland wird zur Bundestrojanerrepublik by Erich Moechel for fm4.ORF.at
All 19 secret services now have a license to use malware. IT security vulnerabilities can therefore be kept open, preventive cyber attacks are the best defense – security expert Manuel Atug on the new German “cybersecurity strategy.”
Since Friday, the “Law to Adapt the Constitutional Protection Law” has been in force in Germany. All 19 federal and state secret services are now allowed to use Trojan malware. Another law is already in the Federal Council, which authorizes the police authorities to use Trojans even before a criminal offense has occurred.
German police and customs authorities have had a legal license to distribute such malware since 2017. At the same time, a new cybersecurity strategy is being worked out which, among other things, stipulates that newly discovered security vulnerabilities are not published but, if necessary, passed on to the ZiTis decryption and federal Trojan authority.
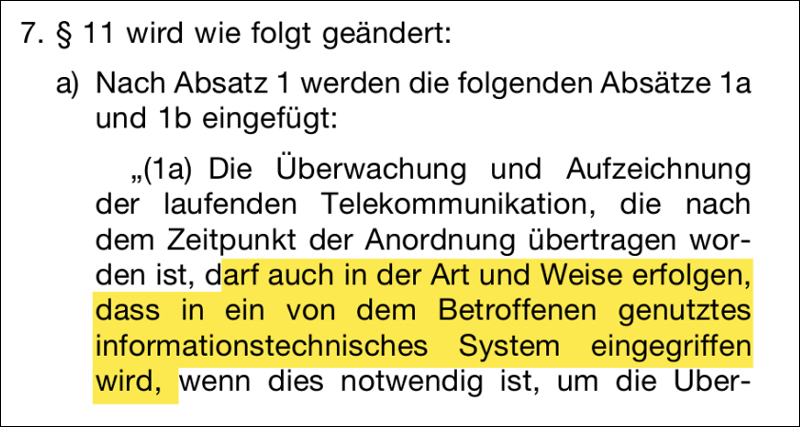
In the German Federal Law Gazette, the federal Trojan is simply called “technical means” and the contamination of a device with malware is described as an “intervention in a technical system”. The “cybersecurity strategy” states it much clearer.
On the one hand security, on the other hand not
In principle, it is true that “recognized weaknesses are generally closed or reported to the manufacturer for this purpose”, it says in terms of content largely right across the new German “cybersecurity strategy”. However, the big “but” comes on page 89 of 128, before the goal of “greatest possible IT security” suddenly a “on the one hand” is placed. Because “on the other hand (there is) the need to enable law enforcement and security authorities to fulfill their legal mandate” and this “tension … must be resolved”.
Here, according to the textbooks of law, in which “balance” plays a central role, attempts are made to ensure security on the one hand, and security must not be guaranteed on the other. The systems should be “a bit insecure so that the forces of good, namely the security authorities, can read along, but expect the forces of evil to adhere to the rules and not use these loopholes for attacks, that’s stupid,” wrote Manuel Atug, IT security expert from the independent working group Kritis, to ORF.at.
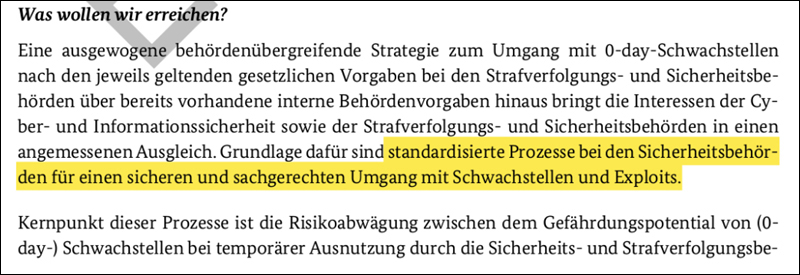
The draft of the cybersecurity strategy for Germany 2021 was drawn up by lawyers from the German Federal Ministry of the Interior, Building and Home Affairs. This passage comes from point 8.3.8 with the title: Promoting the responsible handling of 0-day vulnerabilities and exploits
Compromises between zero and one
“Computers can only deal with the states zero or one and software or cryptography are therefore either secure or not,” Atug continues. The German Ministry of the Interior, on the other hand, is of the opinion that by keeping certain security gaps open “the level of general IT security is increased” by “establishing a binding procedure” that regulates the responsible handling of 0-day vulnerabilities and exploits. “
While the rolling attacks from encryption blackmailers to the actors of unfriendly states are now threatening to destabilize the IT systems of the West through newly discovered and known vulnerabilities, Germany is planning an interinstitutional commission that will decide according to a set of rules whether a certain, newly discovered security vulnerability should be neutralized or kept open for own monitoring purposes. “This assumption is just childish. Cyber space is a large global entity, there are no regional effects here, everything has a global impact, ”comments Atug.
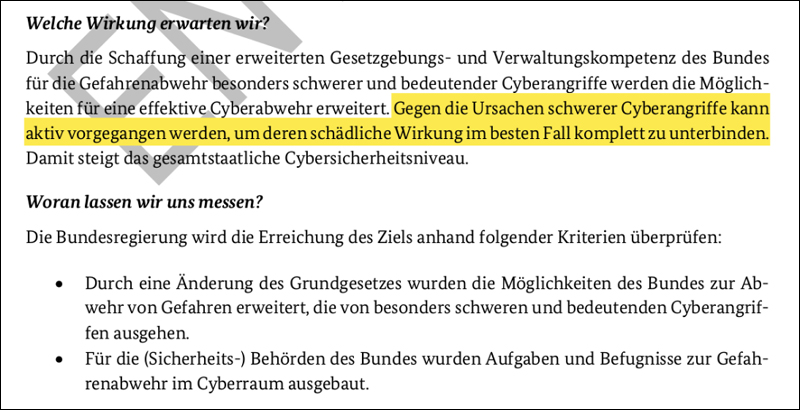
Incidentally, in the same chapter 8.3.8, an amendment to the German constitution, alias the Basic Law, is required, namely the license for preventive attacks on third countries in cyberspace.
Security despite encryption
Cryptography is then discussed in the same Janus-faced manner, for which the well-known slogan “Security through encryption and security despite encryption” must serve again. One of the oldest known sophistic tricks of antiquity is used to bring a word in two different meanings into a sentence. This rhetorical volte was used at the time to “turn a weak argument into a strong one” – according to the Platonic Socrates – and thereby throw the opposing attorney in court.
This scam is now being used by the German Federal Ministry of the Interior to fool the public pretending a legal balance, while the whole technical approach it’s founded on is simply nonsense. But there is a lot more of this, because the “Federal Government’s ability to avert danger in the event of cyberattacks” should also be improved, but how? Quite simply through “the creation of an extended legislative and administrative competence of the federal government for hazard prevention”.
Since there is not much to mention about point 5 for obvious reasons, point 8.3.9 security through encryption and ensuring security despite encryption is recommended for viewing.
Preventive attacks increase security
Indeed, “against the causes of severe cyberattacks” could be “fought actively in order, in the best case scenario, to completely prevent their harmful effects.” It is thus claimed that preventive attacks on IT infrastructures in other countries “increase the national level of cybersecurity (in Germany)”. Probably the most striking example of how this “cybersecurity strategy” came about is a blank sheet of paper in the text that only contains the title “cyber threat situation” and the note “still in progress”.
Manuel Atug: “This is not a strategy at all, because every security strategy has to start from the analysis of a threat situation. As you can see, one is not even clear about the nature of the threat, but on the basis of this ignorance one constructs an entire defense strategy. Furthermore, every strategy has to be free of contradictions, otherwise it does not deserve this name. Here, however, there is contradiction after contradiction, because this is not a strategy, but a hodgepodge of wishes from all security authorities, a ‘make a wish’ under the direction of the Ministry of the Interior. “
Epilogue
If the readership should have noticed that – with the exception of one – all hyperlinks under the screenshots lead to one and the same document, it was done for the purposes of a necessary catharsis. Namely in the hope that one or the other will open the document and read at least parts of it and thus alleviate the suffering of the author and commentator from reading it with pity.
